A recently discovered attack technique poses a significant threat to over 300,000 internet systems utilizing UDP protocols, leaving them susceptible to looped denial-of-service (DoS) attacks. This novel method targets the application layer, specifically affecting systems employing the user datagram protocol (UDP), which lacks request verification due to its connection-less nature.
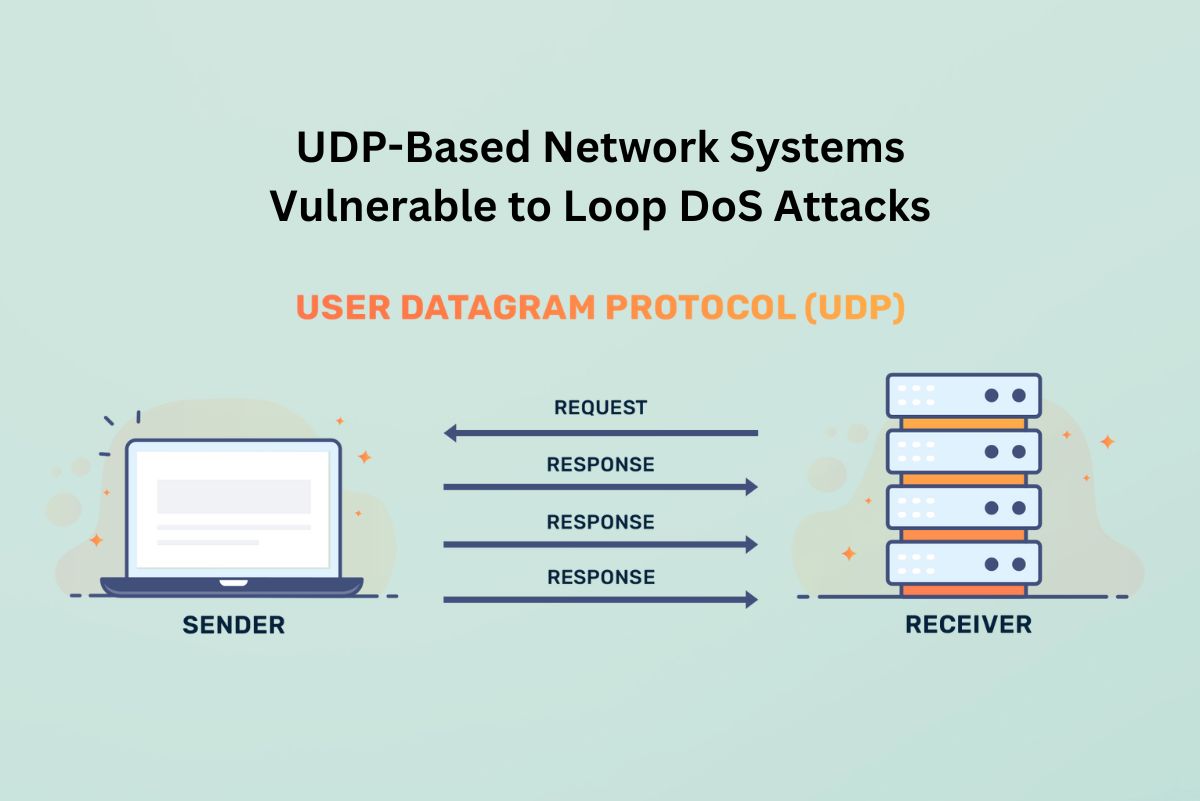
Described as an application-layer attack, the loop DoS attack exploits IP spoofing to initiate a perpetual exchange of messages between two network services. This continuous interaction between the services results in a blockade, effectively denying legitimate access to their respective servers indefinitely.
UDP, designed for rapid data transmission, is utilized for time-sensitive transmissions such as video streaming and DNS lookups. However, its connection-less architecture exposes it to vulnerabilities, making it susceptible to DDoS attacks. The identified vulnerability, tracked as CVE-2024-2169, enables unauthenticated attackers to exploit UDP implementations, leading to Denial of Service (DOS) incidents and resource abuse.
The attack loop begins with a single IP-spoofed error message sent to one of the vulnerable servers, prompting a reciprocal exchange of error messages between the servers. This perpetual communication strain impacts both servers and any network links connecting them.
Legacy protocols like Daytime, Time, Active Users, Echo, Chargen, and QOTD, along with contemporary protocols like TFTP, DNS, and NTP, are affected by this vulnerability at the application layer.
While no known exploits have been reported, the potential impact on nearly 300,000 internet hosts and their associated networks is significant. Christian Rossow, one of the researchers involved in the discovery, emphasizes the urgent need for mitigation measures to prevent potential exploitation.
Implementing additional request validation layers for UDP transmissions or transitioning to more secure transport layer protocols like TCP can help mitigate the risk associated with this vulnerability.